Massive Ransomware Attack Makes the World Wanna Cry
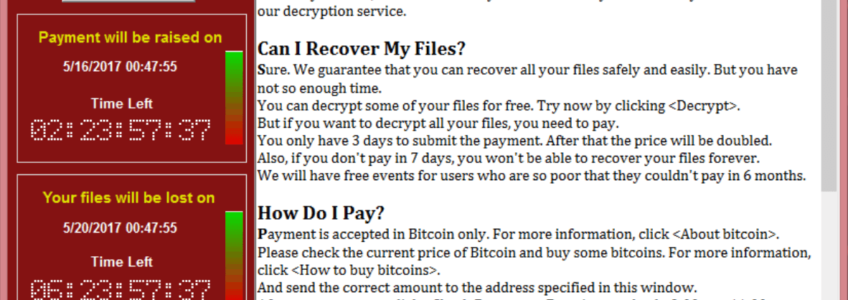
The massive ransomware attack on 100 countries worldwide left the world reeling from the scale of the cyber-attack and pretty much every cyber-security expert saying “told you so“. With a record 126,000 infections, the perpetrators behind the attack reportedly made $26,000 in a 24-hour period.
So how did the hackers manage to infect so many computers all at once? The self-propagating malware used a tool called EternalBlue that exploited a vulnerability in Microsoft operating systems that allegedly was created by the NSA, stolen by TheShadowBrokers, and released to the public in April. Microsoft released a patch for the vulnerability in March but many older systems still in use today remained vulnerable and many organizations do not enable automated updates that would have protected them from this attack. Once a computer on a network was infected, the worm was able to continue spreading through the network from vulnerable computer to vulnerable computer which could account for how quickly the malware spread.
The attack was inadvertently halted on Friday by a security researcher who goes by the name MalwareTech. While analyzing the code, MalwareTech identified an unregistered domain name being referenced and as part of his research into the behavior of the malware, he registered the domain. This action appeared to have acted as a kill-switch for the ransomware, at least temporarily. After directing the domain’s traffic to a server, the server immediately started seeing traffic of 5,000-7,000 hits per second. Unfortunately, there are already new variations of the malware that does not look to the unregistered domain name so it’s vitally important that organizations patch their systems sooner rather than later.
How can you protect against ransomware? This is a question asked all the time and there are some simple things that both individuals and organizations can do to prevent a ransomware attack. First and one of the easiest things to do is to keep your firewalls, operating systems, and anti-virus up-to-date. Whenever possible, enable automatic updates because the time from a vulnerability being discovered by hackers and the time until you patch is your risk factor for being breached/attacked (and one of the core reasons why Axiom developed its SecureAmerica Automated Threat Defense Platform!)
And of course, be wary of unsolicited emails that contain links and attachments. Hackers are getting more clever and finding devious ways to hide their ransomware infections. They are embedding files within files to infect businesses. All it takes is one click of a link or the opening of a file for you to lose access to your vital data.