Does Your Business Have a Security Strategy?
The least expensive cyber-security strategy that a business can have is “If we pretend the problem doesn’t exist, maybe it will just go away.” The most expensive cyber-security strategy a business can have is “If we pretend the problem doesn’t exist, maybe it will just go away.”
Let’s face it, most small businesses started when someone with a great idea and a bit of an entrepreneurial spirit created a product or service that they wanted to get to market as soon as possible. They scraped together as much money as they could, maybe even got some investors on board. They “hired” family members and friends to work until they were finally able to afford to pay them. They worked long days (and nights) looking forward to the day they would ultimately turn a profit.
As they became more successful, things grew, and so did the need for technology to keep their company competitive and viable. Computers were purchased, new technologies were incorporated, more people were hired to operate those, and records moved from paper to electronic media. Data began to accumulate: customers’ information, HR records, invoices, bank statements, credit card numbers, proprietary company information, and intellectual property. At some point, the business became dependent on its technology to the point it was integral to business continuity.
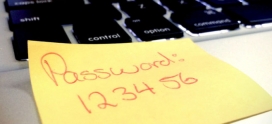
For some out there, maybe all this happened in a few short months while for others it has taken years to grow the business to where it is today. However, all of that can virtually disappear in an instant simply because at the genesis of the business a cyber-security strategy was never an equal priority. In reality, it’s highly unlikely anyone was simultaneously thinking about what firewalls, virus scanners and encryption to use in the push to bring the product or service to market. Any protections that might exist now “just kind of happened” rather than being purposely put in place.
Oddly, though, this is opposite of the mindset of cyber-criminals as they bring their “products and services” to their market. They are completely and purposely focused on taking advantage of this weakness in many small businesses. Their “business” is doing all they can to steal and/or destroy what it has taken years for you to grow. And this they do without regard to the fact that it will destroy the businesses and lives of those they hack.
According to Richard W. Downing, Acting Deputy Assistant Attorney General of the Department of Justice, “We rely more than ever on computer networks, electronic devices, and the Internet in almost every aspect of our lives and businesses. And just as the importance of these technologies has grown, we also face ever more sophisticated and destructive threats to our personal lives and our businesses from hackers, organized criminal networks, and even nation states…. The crimes they commit put individuals and companies alike at risk of financial ruin and undermine the security of our technological infrastructure.”
Ignoring the problem isn’t going to make it go away, but in fact could cost you your business and all you’ve worked for. The businesses that are going to be around in the future are the ones who take seriously today the growing number of threats that exist and make cyber-security a priority.
So what does this look like?
The Federal Trade Commission says:
“Sound security for businesses means regular risk assessment, effective coordination and oversight, and prompt response to new developments. Basic steps in information security planning include:
- identifying internal and external risks to the security, confidentiality and integrity of your customers’ personal information;
- designing and implementing safeguards to control the risks;
- periodically monitoring and testing the safeguards to be sure they are working effectively;
- adjusting your security plan according to the results of testing, changes in operations or other circumstances that might impact information security; and
- overseeing the information handling practices of service providers and business partners who have access to the personal information. If you give another organization access to your records or computer network, you should make sure they have good security programs too.
As larger companies take steps to secure their systems, less secure small businesses are easier targets for cyber criminals. So for businesses who want to take this more seriously, the Federal Communications Commission has produced a 51-page Cyber Security Planning Guide which will help you map out a strategy to protect what you’ve worked to create.
Keep in mind, too, that cyber-security is more than an “IT assignment” and that most IT personnel do not specialize in cyber-security. And since many small businesses don’t have the staff and resources to adequately protect themselves, you may need to consider working with companies that provide specialized, managed cyber-security services. If you would like to discuss how we at Axiom Cyber Solutions can help you in this, give me a call at 800-519-5070 ext. 717, or email me at ben.johnson@axiomcyber.com.