Back-to-School Cybersecurity: What College Students Need to Know
“It’s that time of year again.”
Everyone is so original with their ad campaigns around this time of year. Nevertheless, August means that millions of students across the country will be going back to school. Among them, an astonishing 20.5 million university and college students will or already have started back in full force for the Fall 2016 semester in the U.S. alone. From seniors itching to graduate to wide-eyed freshmen trying to take it all in, universities are about to be jam packed with bodies eager to learn and have fun.
Amid the countless things packed in the bags of these students, a laptop, tablet, or some other sort of computer is essential for almost every single class, be it in-class or online. While the online components of college classes allow for more open communication between students, peers, and professors, there are some drawbacks to having all of these people online. Even though college-age students are generally more tech savvy than most other demographics, hackers and cybercriminals are targeting both the students and institutions alike more and more aggressively and there is a myriad of cyber threats that are trying to hurt or steal these students’ personal information.
Unsecured Public Wi-Fi Connections
While it is an incredibly convenient thing for students to be able to be connected on campus via free Wi-Fi, it could also potentially be extremely dangerous. The use of any public Wi-Fi connection, be it at the library, coffee shop, or anywhere else on or around campus, can be very risky because these networks are very rarely secured properly and consequently are a big target for cyberattack. Due of the openness of the connection, almost anyone who knows how could view what you are doing online while you’re connected.
The best way to avoid this threat is to not use unsecured public Wi-Fi. While this is a nice thought, it is not necessarily a realistic solution for all students, especially those that live on-campus. If you must use an insecure public Wi-Fi connection, make sure to not unveil any personal or financial information and only use secure, encrypted sites. Most universities do offer separate secure networks with a unique login for each student that is usually made up of either the individual’s student ID number, email address, or some other personal identifier. If your university offers such a connection, this is the best route to take.
Phishing Scams
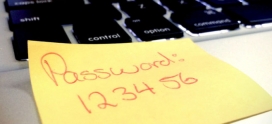
Phishing attacks target different groups of people for different reasons. Email phishing scams that target college students are usually designed to try and steal personal information such as account names, passwords, and banking information.
The threat of phishing has been a big issue for North Carolina State University for several years now. N.C. State has seen rather targeted attacks where cybercriminals have performed reconnaissance to make their messages seem more realistic to students. Scammers have created virtually perfect copies of multiple N.C. State login pages with reference to the university and other specifics related to specific students’ involvement. With hackers working diligently to make their schemes appear legitimate, it is extremely important that students take defensive action against phishing scams into their own hands.
The first defense against phishing attacks is knowing how to identify them. If the message has an urgent request or is poorly worded, it is likely to be a phishing email. One thing that is fairly consistent in all emails of this nature is that they include a malicious link that appears to be legitimate. Students can verify the authenticity of a link by hovering his/her mouse over it. Scammers want to appear as true-to-the-original as possible, and will often use logos they find online. Examine these images to see if they are of the professional quality that your university would actually use, and this could be helpful in indicating a false sender.
The best plan of attack for combatting phishing emails is to not open any email from a strange, unrecognized source and report the incident to your university immediately so that your peers do not fall victim to this same scam.
Sextortion and Webcam Hacking
While it is pretty scary to lose your important personal and financial data, it is even more terrifying to have a cybercriminal harassing you by threatening to expose sexually explicit photos of you all over the internet unless you pay up or give them more photos. This cybercrime is called sextortion and some of its primarily targets are young people, specifically young women.
In May of this year, two students at George Mason University in Virginia reported to police that they were the victims of sextortion. Both victims claimed that their respective “sextortionists” demanded a $5,000 payment in lieu of him exposing the compromising photos online. This is a threat that the FBI says is increasingly growing and is in desperate need of being stopped.
There are a few ways to help combat this cybercrime:
- Don’t send explicit photos of yourself to anyone.
- Do not talk to people you don’t know personally online.
- Turn off or cover your webcam when not in use—many cases of sextortion happen even if the victim has never sent out explicit photos. Hackers get into a person’s webcam and snap pictures without the target ever suspecting it. Just a piece of tape over the camera can be the difference between being safe or becoming a victim of sextortion.
Universities themselves are fighting cybercrimes like data breaches and ransomware that are targeting the student body as a whole—putting your and your classmates’ information in danger. Because of this, it is important for you to take your cybersecurity protection into your own hands. By taking a few simple steps, you can protect yourself against lurking hackers in a café, scammers trying to steal your information via phishing emails, and sextortionists who only want the worst out of you. When you protect your personal cybersecurity, you can truly enjoy the best years of your life without worrying about your personal data.
Hailey R. Carlson | Axiom Cyber Solutions | 8/25/2016