Cyber Security: Not a Priority in Nuclear Power Plant Facilities
October is National Cyber Security Awareness Month. In our past articles, we’ve mentioned cyber security vulnerabilities ranging from both small to large businesses, healthcare organizations, and more. Recently, a report was published by the International Policy Institute, Chatham House, on cyber security in nuclear power plants.
The fifty-plus page report was released this past September and detailed numerous shortcomings found in worldwide nuclear power facilities, including the United States. The report was extremely critical of vulnerabilities found in these facilities. Many of these infrastructures are ‘insecure by design’, because of their age and are not as well prepared as they may believe. In fact, many of these infrastructures were built before cyber attacks were even considered.
Recent high profile cyber attacks have brought to light these cyber security vulnerabilities in nuclear facilities. Couple that with the present rising number of crimes perpetrated by cyber criminals and terrorist groups and the very real fear of releasing radiation, you have a real cause for concern.
The report states that their focus is on when a plant’s control systems are “disrupted or even captured and harnessed by saboteurs acting either inside or outside the facilities where these systems are located.”
The range of threats could vary from stealing confidential corporate data for financial profit or stealing operational information to be used in an attack at a later time. Considering a plant’s industrial control system, the report states,
“A cyber attack that took one or more nuclear facilities offline could, in a very short time, remove a significant base component to the grid, causing instability.”
However, the worst case scenario according to Chatham is an attack on a nuclear plant’s backup power system could cause a release of ionizing radiation.
Chatham studied nuclear power plants worldwide over an 18 month time period. They found several factors for these vulnerabilities and we have narrowed down the following four industry-wide cyber security challenges.
1. Employees and Human Nature: In general, poor IT practices and the very human nature of finding shortcuts at work can contribute to security breaches. For example, employees may want to charge their smartphones by directly charging them in a control computer but if these devices lack antivirus software, systems are particularly vulnerable.
One source goes on to describe how in some US nuclear power plants, engineers will bring in their personal computers into work, plugging them directly into the computer interface of the PLC (Programmable logic controller). If the engineer’s personal computer is infected with malware, it can and will affect the PLC in the process.
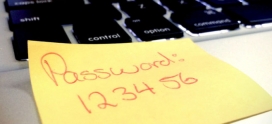
2. Passwords: Default passwords are commonly found at plant facilities, according to Chatham’s report.
“The failure to change default passwords is another challenge at nuclear facilities. In some instances, nuclear facilities fail to take basic ‘good IT hygiene’ security measures, such as changing the factory default passwords on equipment.”
It’s incredible how such a simple safety measure is being overlooked. This is part of a bigger problem, which leads us to our next item.
3. Culture of denial: One source explained that there is a ‘culture of denial; found in many nuclear facility personnel,
“It remains a movie scenario, maybe in the future. They think it is just states against states, not everybody wants to hack us, and also it won’t happen here.” Although many personnel feel it’s unlikely, cyber attacks need to be considered as a real threat. Harmful radiation would have everlasting effects.
Chatham found that cyber security training lacks a cohesiveness in drills between regular plant personnel and the IT security personnel. Training includes focusing on more reactive than proactive solutions, so in many cases, cyber attacks are occurring before an employee is aware of it.
4. Air gaps myth: An air gap is a network security measure, employed on one or more computers to ensure that a secure computer network is physically isolated from unsecured networks, such as the public Internet or an unsecured local area network. Many in the industry believe that ‘air gaps’ will keep them safe from cyber attacks but in reality, all nuclear plants are not ‘air gapped.’
The issues is that employees want those ‘commercial benefits’ that the Internet can offer, and don’t consider that they are connected to the internet.
“A number of nuclear facilities now have VPN connections installed, which facility operators are sometimes unaware of,” the report says. VPNs can be used to introduce malware onto the industrial control network.
Something as tiny and simple as a flash drive is all it takes to gain access into a plant’s system, personal computers are used frequently enough and because they can be directly connected to a plant’s control system, it is by no means a guarantee.
Chatham concludes that “plants must develop guidelines to measure cyber security risk in the nuclear industry, including an integrated risk assessment that takes both security and safety measures into account as well as fostering partnerships between vendors and cyber security companies to enable the development of more robust cyber security products.” Getting a handle on practicing ‘good IT hygiene’ as we mentioned earlier is also an element that needs to be addressed at all of these facilities.
Axiom’s solutions come in different sizes and all Axiom solutions are designed to deal with the attack vectors of today while being adaptive and flexible enough to continue to secure your network for years to come. For more information, give us a call us at (800) 519-5070.