Between tight budgets and simply having too many other things to worry about, SME owners often overlook cybersecurity. The thought is that because the company is so small, no hacker would waste his or her time trying to gain access to the information you possess.
This logic is simply wrong. Around half of the cyber attacks that occur each year are on small businesses, and this number is expected to grow in the future. Ignoring cybersecurity is taking on an unnecessary risk for your business that could cost you big time down the road.
But why do hackers target SMEs? It is true they have a lot less information, and hacking into a large corporation stands to be a lot more lucrative. Well, the simple answer is that they are just easier targets. They know that a lot of small businesses don’t consider themselves worthy of hackers’ attention, and they know they have a better chance of stealing information and getting away with it. To hack into a larger company, hackers would need to bypass much more advanced security measures. They are often unsuccessful in doing this, so going after SMEs ends up being the better move.
Plus, just because your business is small doesn’t mean that it doesn’t have valuable information. Credit card data, identification numbers, mobile phone numbers, etc. are all worth something, and if a hacker can steal this information from enough companies, they can sell it and make a fair bit of money. So perhaps the real question is why wouldn’t hackers target SMEs?
If this isn’t enough to convince you to take cybersecurity seriously, consider the consequences that this decision can have on your business.
Reputation damage
Often times, one of the things that helps a small business stand out from the competition is its reputation and relationship with customers. People are more likely to trust small companies, and are usually more loyal to them because of this.
However, if you lose people’s data and expose them to unnecessary cybersecurity threats, this trust will be gone in no time, and you may not be able to convince them to come back to you. This damage to your reputation could be the eventual downfall of your entire business.
Recovery is expensive
Beyond just the damage a cyber attack would do to your reputation, you will also be facing a steep financial hill. You may need to pay retributions to customers for lost data, and there is a chance you will face lawsuits, which are always expensive.
This alone could be enough to send your business under, and that is not even counting all the time and resources you’ll have to dedicate to cleaning up from an attack. Diverting energy away from core business functions can run you into the ground quickly. It is no wonder 60 percent of all small businesses fail within six months of a cyber attack.
Lost value
There may come a day when you decide to sell your business. And when determining the value of your company, investors will look at how well you account for and mitigate risks. If you’ve been the victim of a cyber attack, or if you do not have a good plan in place for them, this will reflect negatively on the value of your business, causing investors to give you a much lower valuation, or perhaps even walk away without making an offer.
It just makes good business sense
It really comes down to this. You wouldn’t leave the front door of your home or office unlocked so that anyone who wants to steal from you can just walk in whenever they want. So why would you leave your business unprotected from cyber threats? It may require some extra time and a little investment, but this is well worth it considering the alternative may mean going out of business and losing everything.
About the author: Jock is an entrepreneur who has built and sold several online businesses throughout his career, including a website dedicated to home and business internet security. Connect with Jock on LinkedIn here.



 There is a real issue with cybersecurity alert fatigue. It is such a problem that TechRepublic ran an article titled “
There is a real issue with cybersecurity alert fatigue. It is such a problem that TechRepublic ran an article titled “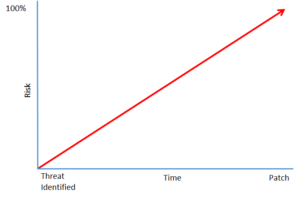 And if cybersecurity teams, or the lone IT professional tasked with anything & everything within the organization (including cybersecurity, which is not a hobby), are overwhelmed, what does that mean for the cybersecurity defense of the organisation? Troy Wilkinson, CEO of Axiom Cyber Solutions, has frequently discussed that a company’s risk factor exponentially increases from the time that a vulnerability is disclosed to the time that a patch is applied yet still so many organizations are struggling to stay on top of their cybersecurity defense.
And if cybersecurity teams, or the lone IT professional tasked with anything & everything within the organization (including cybersecurity, which is not a hobby), are overwhelmed, what does that mean for the cybersecurity defense of the organisation? Troy Wilkinson, CEO of Axiom Cyber Solutions, has frequently discussed that a company’s risk factor exponentially increases from the time that a vulnerability is disclosed to the time that a patch is applied yet still so many organizations are struggling to stay on top of their cybersecurity defense.